In recent times, cryptocurrency mining has exponentially increased both as a topic and an activity. All this can be attributed to the surge of crypto in the last few years.
Crypto mining involves a series of computational processes to earn crypto. Usually, the mining process requires high amounts of computing power – with more computing power translating to more gains.
As a result, individuals have come up with ingenious ways – both honest and dishonest, to acquire more computing power. One of the honest ones is joining a mining pool. Another not so honest one is botnet mining.
Botnet mining is one of several ways that black hat hackers continue to commandeer unsuspecting users’ computing power to mine cryptocurrency. It’s a rather novel, yet highly effective way for cyber hackers to earn crypto without breaking a sweat.
What’s Botnet Mining?
A botnet is a collection of various internet-connected devices, ranging from desktops to PCs to mobile phones to IoT devices – injected with malicious software and then controlled by the malware from that point on. The owners of these devices are seldom aware that their machines are being controlled by foreign software. A botnet enables the malware owner to get a payday at the oblivious devices’ owners’ expense.
How Do Botnets Work?
Botnets are automated computer programs specifically designed to corrupt a computer system to the liking of its creator. The malware surreptitiously sneaks into the victims’ device and utilizes the devices’ computing power, internet bandwidth, electricity to mine crypto. The malware is purposefully engineered to infect any device that plugs into the same network. The computing power of all these devices is then harnessed to mine even more cryptocurrency. A high computational power tremendously boosts the mining output, resulting in more earnings for the malware owner(s).
What Are Some Examples of Mining Botnets?
As the practice gains a foothold, several botnets have cropped up over the years. However, some have managed to stick out just for their notoriety. Here, let’s have a look at three of the most famous mining botnets:
#1. Smominru Botnet
Created in May 2017, the Smominru miner botnet is estimated to have mined over 9,000 Monero coins worth more than $3.6 million at the time of writing. Within a span of slightly over three years, Smominru has infected more than 600,000 devices.
Smominru miner botnet is observed to have spread to a global scale, with the majority of its presence being in Russian, Taiwan, Brazil, and India. Its regenerating nature has made it quite elusive to contain despite multiple efforts. This is because the malware creators, suspected to be based in China, keep registering new domains after the old ones are banned.
Monero seems to be the most preferred coin by the Botnet, thanks to its anonymity and privacy-oriented features, which make it hard to track the destination address of the mined coins.
#2. DDG Botnet
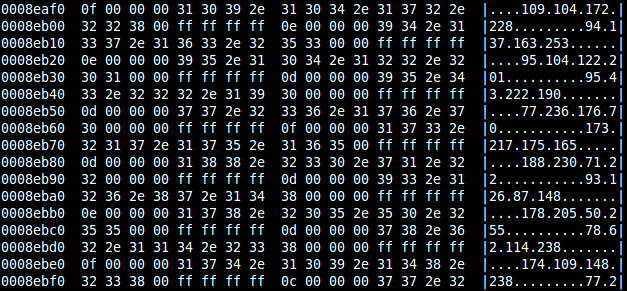
Created in March 2017, the DDG botnet has mined in excess of $1.5 million worth of Moreno. To date, it has infected over 4,000 devices harnessing their collective processing power. The DDG botnet utilizes OrientDB and Redis servers because these have more CPU than the average PC.
DDG was created specifically to target servers. The 4,000 target devices accumulate Redis and OrientDB database servers. The majority of the infiltrated servers are located in China and the US, with the rest scattered across the globe.
Studies show DDG uses a script called i.sh that makes the Botnet’sBotnet’s architecture super flexible. This feature allows the malware creator(s) to download and infect vulnerable servers with it.
#3. ADB.Miner
The ADB. Miner botnet was discovered in the early months of 2018. This BotnetBotnet is unique since it’s coded to target Android devices to mine, Monero.
The creators of this botnet aim at compensating the low CPU power in phones with a large target scope. It is estimated to have infected more than 6,000 devices within the first few days, with this figure doubling every 12 hours.
What’s more, the creators are also targeting smart TVs that have more processing power than phones. The BotnetBotnet infects a device through port 5555. This port is deployed by the command-line software Android Debug Bridge. By default, port 5555 is usually disabled on all Android devices. As such, only users who manually enable it risk the breach.
The vast majority of ADB.Miner botnet victims are in China and South Korea.
Huge Gains for Little Effort?
Mining cryptocurrency legitimately is complicated and intensive work. Therefore, botnet mining is becoming more popular with cybercriminals since it’s less risky and offers huge returns. The botnets programs are automated; thus, so little work is put into it.
We already established that botnets have massive returns. And as of now, there isn’t exactly a viable plan in place to contain the menace. VP of Threat Operations told News.com.au that “Taking down the botnet is very difficult given its distributed nature and the persistence of its operators.” In this state of affairs, botnets are set to increase, and with them, their ill effects.
Crypto Scammers Leverage the COVID Pandemic
The majority of these botnets gain access to their targets’ devices using undetected methods. The most common methods are embedding malicious code in a link sent as an email. Victims are enticed to click on the link based on the content of the email. Secondly, computer users who are not exactly tech-savvy are, in more ways than one, negligent to the importance of cybersecurity. Therefore, they leave their devices open for hacking.
In this COVID-19 season, cyber crooks are taking advantage of unsuspecting internet users more than ever. They are now impersonating health bodies such as the World Health Organisation so that when users visit such a site, they’re redirected to potentially click on malicious links that could trap them in a botnet and other scams of the nature. As an internet user, being aware of such malicious intentions is the first step to avoiding them.
Final Thoughts
As otherworldly as the concept seems, botnets are real, and the tech world is yet to come up with ways to tackle them. It’s almost impossible to contain one at the individual level, but keeping an eye on the various processes your device is running should go a long way.